Who We Are
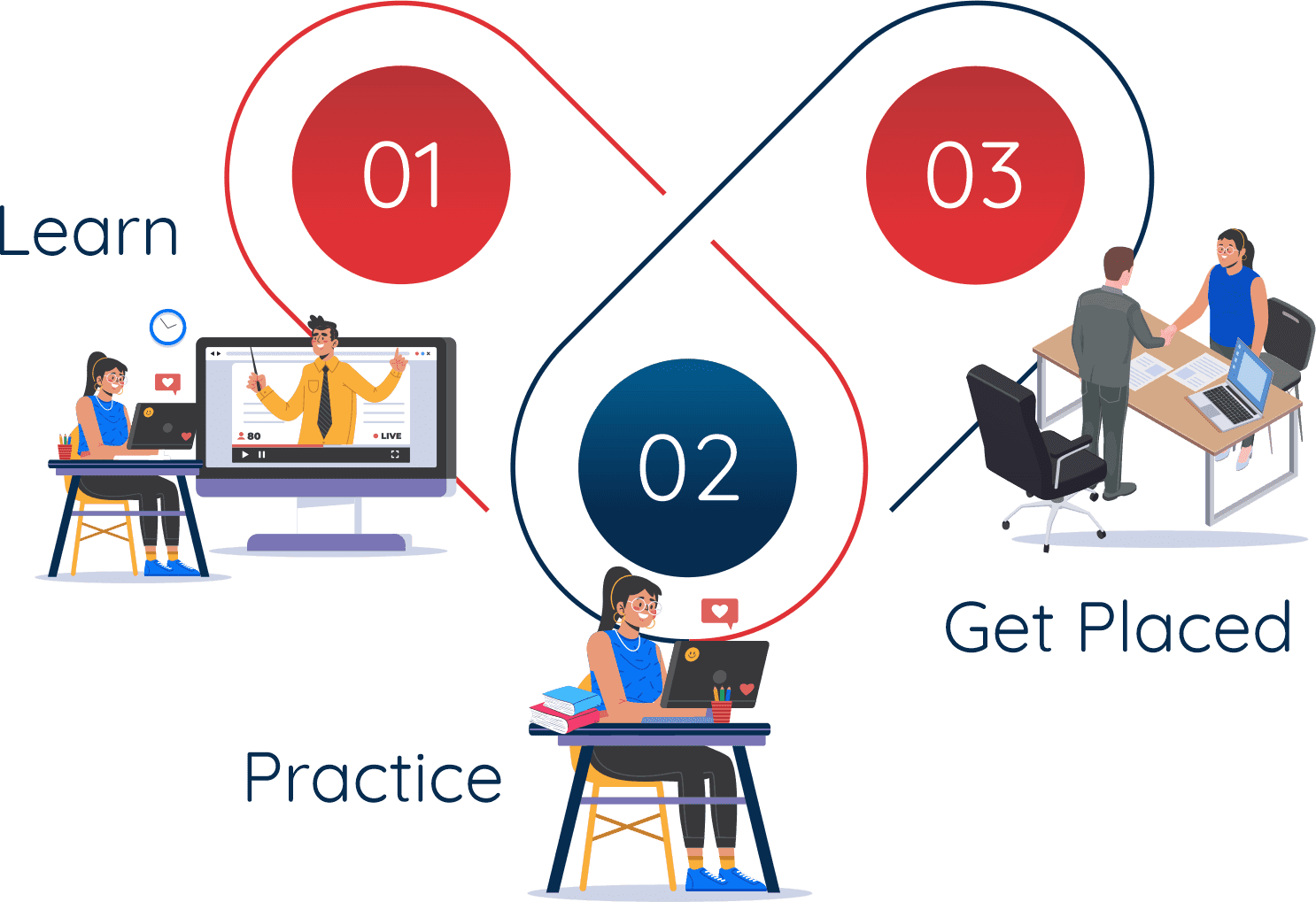
Cyber Sec Guru is the leading IT company in Ludhiana offering professional services & training since 2013
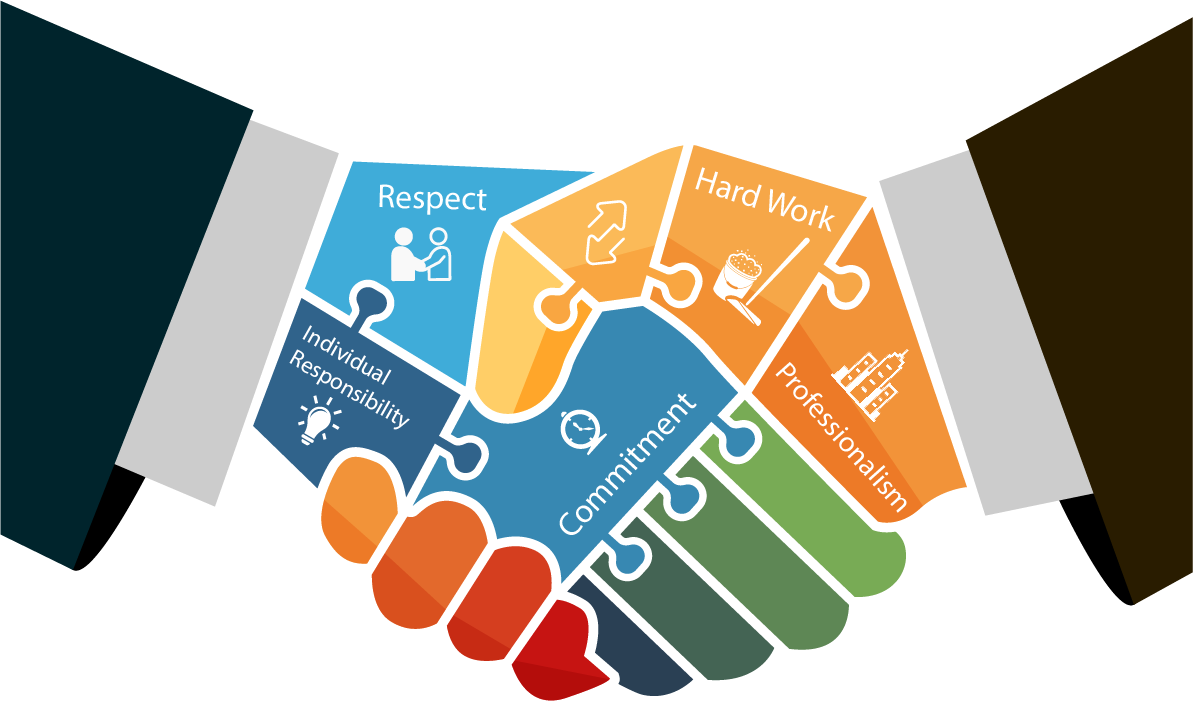
Cyber SecGuru is an organization which fulfills the need of technology based risk management & cyber security solution across the globe. Cyber SecGuru as a unit of Data Security Robot Educational Management and Research Foundation aims to provide cyber security solutions to private and government organizations across the globe. With around 200+ clients across the globe CSG aims at providing Vulnerability Assessment, Penetration Testing, Digital Forensic Investigation services making cyber security convenient for every organization & cyber crime free world.